POIPU, Kauai—Credit union board members gathered here were warned about just how many “doorways” there are into CU systems, how they are opened and how they can be locked, while also being pointed toward a free security tool every CU should be using.
Speaking to Rochdale’s Volunteer Leadership Institute (VLI), Randy Romes, a principal with CliftonLarsonAllen LLP, shared with attendees a graphic showing all of the devices in their homes and lives—from routers to refrigerators—that are part of the Internet of Things, and said the same applies to credit unions, which are much juicier targets for bad actors.
All devices include software, software is written by people, and all software has flaws, Romes said, reminding attendees that the major 2013 breach at Target occurred after fraudsters entered its systems through software that ran refrigeration units in its stores.
“There is risk here, but too often when there is risk, people think it’s bad and they run away from it,” he said. “In risk we have opportunity. It’s a balancing act, and we have to balance it.”
Borrowing the Boy Scout Motto
Romes, who has spent 27 years working as a white-hat hacker, repeatedly invoked the Boy Scout motto of “Be Prepared” in urging boards to ensure their credit unions are investing in IT security and training for IT staff, as well as ensuring security audits are being performed.
Citing IBM’s Data Breach Report, Romes said the average breach lasts 241 days, including an average of 181 days to identify an attack and another 60 days to contain it.
“That’s a lot of time for bad guys to be poking around in a credit union’s systems,” he said.
“What are the bad guys doing when inside the system? They are stealing. They are monetizing their access. They are trying to figure out what to do with your information and with the access that can lead to money.”
The average cost of a data breach was $4.4 million to organizations in 2025, Romes said, noting many breaches are significantly more expensive.
Threats in the Cloud
With most organizations having moved their email solutions to the cloud—particularly Microsoft Office 365—it is no surprise fraud attempts frequently target login and password credentials, Romes said. For that reason, it is common for credit unions and businesses to regularly phish-test their own users as part of their security programs.
“Your IT people will say there is no problem,” Romes said. “The problem is whether your people are very good at recognizing your phishing service’s phishing messages.”

At CLA, he said about 5% of its 9,000 employees—who are phish-tested every month—fail the test, amounting to roughly 450 employees.
“These phishing services track up to the click, but they don’t understand the ‘so what’ factor,” Romes said. “You get by the multifactor and you get access to the VPN portal. And you may not be testing the right controls anymore. You want to understand the controls before the email ever gets to the user. Phishing services test the middle user, and then they need to test what happens when they fail.”
‘Super Serious’
“This is super serious,” he added. “You need to regularly and aggressively test your people. They are core to the control matrix.”
Romes said credentialed phishing schemes are on the rise and indiscriminately target all inboxes, noting that more than 700 million phishing emails are blocked each week.
Romes said the culture within a credit union is critically important in the event someone is successfully phished.
“Bad actors typically don’t know for an hour that they have penetrated a system,” Romes said. “We need a culture of security where people own up to this stuff. Call someone right away and get the password changed. Nineteen times out of 20, an hour later the bad guys get in.”
One Credit Union’s Experience
He shared the story of one credit union whose controller appeared to send an email to AP instructing it to process a payment. IT changed the controller’s password immediately, and when reviewing the login files they were able to see logins from the bad actor.
While deleted emails should continue to exist on a system for up to 90 days, Romes noted that in this case, when the supervisory committee learned of the incident and asked for an independent investigation, it found log retention had been set to the default 30 days—meaning less opportunity to examine the breach.
In this case, the fraudster was located in Ukraine.
“The bad actors had been attempting to log in for almost three weeks before accessing the account, including activity on weekends,” Romes said, noting the IT department should have flagged the unusual activity.
Working Weekends
“By logging in on weekends, even if the fraudster is locked out, it reduces the likelihood that the email accountholder will know,” Romes explained.
The fraudster was ultimately able to access eight years’ worth of email, as well as the accountholder’s contacts, calendar and more. The analysis found the fraudster accessed emails containing 87,884 credit card numbers and 51,071 Social Security numbers.
He shared another example of a credit union in which fraudsters took five terabytes of information, underscoring the need for credit unions to monitor data outflows.
Preventative Measures
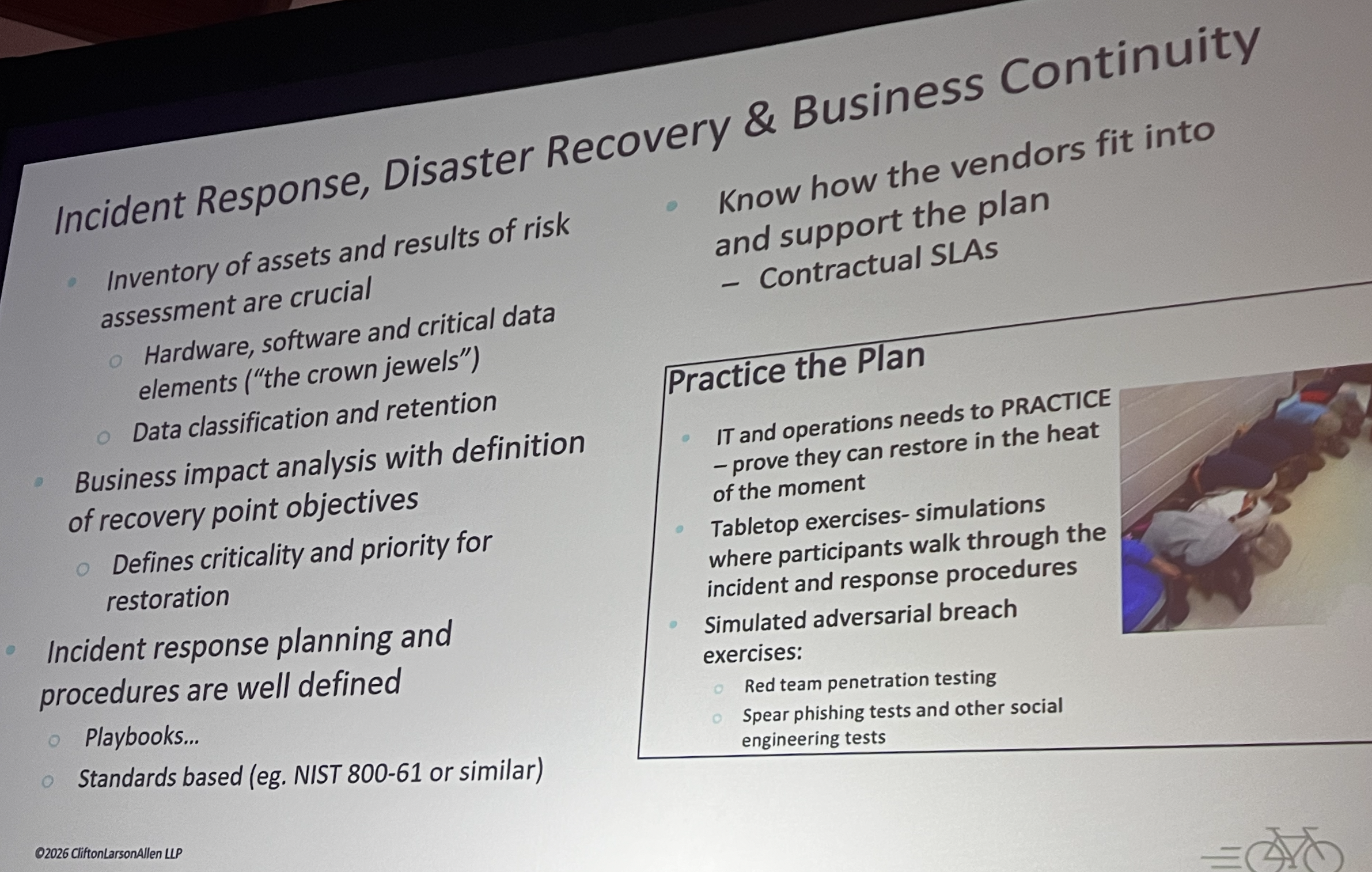
Romes urged CU volunteers to ensure that when it comes to data security, their credit unions need to:
• Improve monitoring
• Improve password security requirements (many are “stupid simple”)
• Enforce multi-factor authentication on all forms of remote access
• Implement geo-restrictions to Microsoft 365
• Enable email log retention settings
• With Microsoft 365 licensing, make sure the credit union has E5 licensing. It’s expensive, he acknowledged, before recommending, “You need to find a way to fund this.”
Threat from Lazy Programming

Romes further reminded attendees that the Java coding language is very common, and that many programmers are lazy and, when writing applications, often grab code from GitHub that contains vulnerabilities.
“That’s a problem from a supply chain perspective because it’s built into everything. It’s different from the way vulnerabilities exist in firewalls, routers, switches and printers,” he said.
He cautioned that it is critical for all IT infrastructure to be well documented. If not, and a breach occurs, the credit union will not know what to do, will not know if it is vulnerable, and will not know who to contact to obtain a fix.
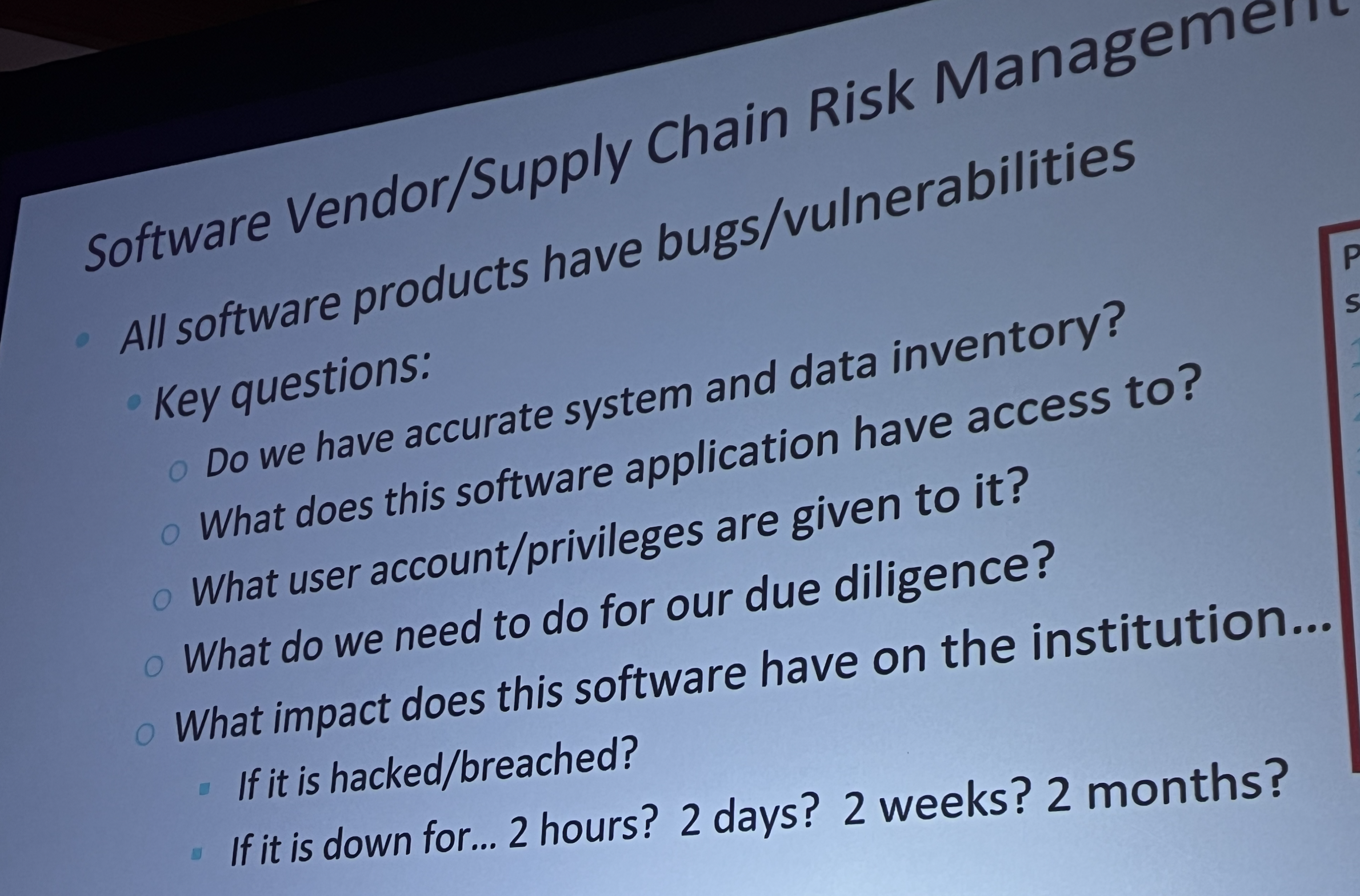
Key Questions
Other key questions to ask, Romes told the VLI meeting, include:
• Do we have accurate systems and data inventories?
• What does this software application have access to?
• What user accounts and privileges are given to it?
• What do we need to do for due diligence?
• What impact does this software have on the institution if it is hacked or breached, or if the credit union is down for hours or months?
• Has the credit union performed a ransomware readiness or resilience test?
• Can IT operations be restored from bare metal up, in the heat of the moment?
• Are you confident your hosted vendor is prepared?
Romes told board members that a credit union also needs to have management authorities identified in the event of a breach.
“Who is authorized to make decisions?” such as shutting down the website, he asked.
Where to Go for Help
Romes recommended that even the smallest credit unions turn to CIS Critical Security Controls, version 8, which include resources such as checklists, benchmarks, reporting and tracking tools, and other guidance.
“The roadmap is already there,” he said. “This is the best, plain-English framework out there.”