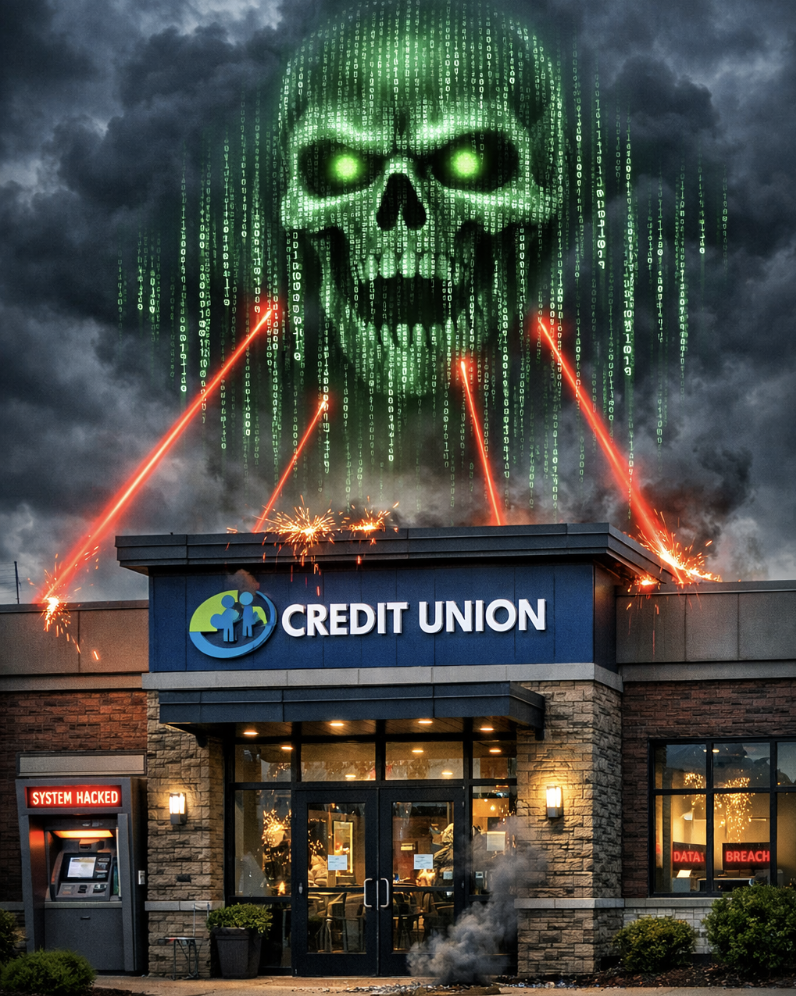
WASHINGTON— U.S. financial institutions are stepping up cybersecurity monitoring and defensive measures amid warnings that Iran-linked hackers could target American banks and financial infrastructure following recent U.S. and Israeli military strikes on Iran, according to government officials, industry groups and cybersecurity experts.
In a statement to the CU Daily, Rahul Powar, CEO of Red Sift, a provider of cybersecurity solutions, said, “During periods of heightened geopolitical tension, financial institutes, including banks are often the first target. Attacks often come in two forms, obtaining information, or service disruption. Both have a direct impact on markets, and customer trust. As escalations increase, there has never been a more serious time to take preventative measures. Institutions that lack protection leave their domains open to spoofing, fueling phishing, account takeovers, and payment fraud at scale.
“Implementing basic measures against impersonation prevention, while strengthening email authentication with DMARC can close the door on bad actors,” Powar continued. “Email remains the primary entry point for attackers, banks must assume elevated risk now and lock down identity, email authentication, and incident‑response readiness before attacks reach customers.””
Close Monitoring
Executives and analysts told Reuters that the U.S. financial services sector has moved to heightened alert status as geopolitical tensions increase, with firms closely monitoring networks for suspicious activity that often accompanies major international conflicts.
The concern stems in large part from the role the financial sector plays in the U.S. economy, involving everything from payment systems, trading platforms and Treasury-market settlement networks.
According to Reuters, a recent U.S. intelligence assessment warned that Iran and its proxies could retaliate against American interests through cyber operations following the escalation of the conflict and the reported death of Iranian Supreme Leader Ayatollah Ali Khamenei in a military strike.
Most Likely Scenario
The Department of Homeland Security assessment said the most likely scenario would involve “low-level” cyber activity such as website defacements and distributed denial-of-service (DDoS) attacks carried out by Iran-aligned hacktivists seeking to disrupt networks or demonstrate retaliation.
Cybersecurity analysts say such operations are consistent with Iran’s longstanding strategy of using cyber tools as an asymmetric response to military or economic pressure, Reuters added.
Increased Monitoring Urged
Industry groups including the Securities Industry and Financial Markets Association (SIFMA) and the Financial Services Information Sharing and Analysis Center (FS-ISAC) have urged financial institutions to increase monitoring, share threat intelligence and prepare response plans.
Todd Klessman, managing director for financial services cyber and technology at SIFMA, told Reuters the industry “remains vigilant and ready to respond to cyber threats,” particularly when geopolitical risks escalate.
Risk From Hacktivists
Security analysts say attacks may come not only from state-directed cyber units but also from loosely affiliated hacktivist groups sympathetic to Iran.Such groups have historically targeted energy companies, financial institutions and government networks, often seeking to cause economic disruption or public embarrassment rather than permanent infrastructure damage, according to cybersecurity experts cited by The Wall Street Journal.